IJCST ONLINE
DOWNLOADS
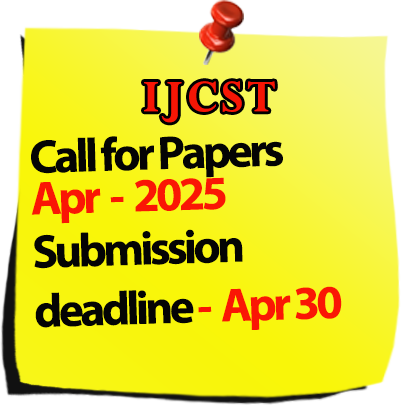
Call for Paper :

Welcomes Conference Proposals

International Journal of Computer Science Trends and Technology
IJCST-Volume 2 Issue 4 / July-Aug 2014
|
S.No
|
Title/Author Name
|
Page No
|
|
1
|
An Efficient Recommender System using Hierarchical Clustering Algorithm
-Prabhat Kumar, Sherry Chalotra Abstract |
1 |
|
2
|
Design and Development of Data Mining System to Analyze Cars using Improved ID3 with TkNN Clustering Algorithm
-M.Jayakameswaraiah, Prof.S.Ramakrishna Abstract |
7 |
|
3
|
Eye Detection Using Area Analysis of Connected Components Which Uses the Concept of RGB Color Based Model and Morphological Operation
-Mrs. Sunita Roy, Prof. Samir K. Bandyopadhyay Abstract |
17 |
|
4
|
Genetic Algorithm Tuned SVM Classifier for Weed Species Recognition
-W.K Wong, Ali Chekima, Muralindran Mariappan, Brendan Khoo, Manimehala Nadarajan Abstract |
24 |
|
5
|
Intrusion Detection Based On Artificial Intelligence Technique
-Shefali Singh, Dr. Zubair Khan, Krati Saxena Abstract |
31 |
|
6
|
Diagnosis of Diabetes Mellitus using K Nearest Neighbor Algorithm
-Krati Saxena, Dr. Zubair Khan, Shefali Singh Abstract |
36 |
|
7
|
Improving Resource Allocation in Virtualized Cloud Environment
-Nisha Sharma, Mamta Dhanda Abstract |
44 |
|
8
|
Pareto Type II Software Reliability Growth Model– An Order Statistics Approach
-Sita Kumari. Kotha, R.Satya Prasad Abstract |
49 |
|
9
|
Monitoring and Detecting Vehicle Based On Accelerometer and MEMS Using GSM and GPS Technologies
-B.Sulochana, B.A.Sarath Manohar Babu Abstract |
55 |
|
10
|
Image Compression a Learning Approach: Survey
-Neelam, Ashu Bansal Abstract |
60 |
|
11
|
Protected Data Distribution for Multiple Owners in Dynamic Groups of Public Clouds
-P.J.Thangamani, G.Nagalakshmi Abstract |
67 |
|
12
|
An Efficient Secure Discover-Predict-Deliver Information Sharing Scheme in Peer to Peer Networks
-T.Mohan Krishna, V.Sucharita Abstract |
73 |
|
13
|
Data Security for Multi Users in Cloud by Using Cryptography Technique
-S.Santhosh, K.MadhuBabu Abstract |
80 |
|
14
|
An Understanding of Mobile Presence Server with Enhanced Scalability in Presence Cloud
-N.Tejesh, D.Prasanth Abstract |
84 |
|
15
|
Image Clustering Using Evolutionary Computation Techniques
-I.Ravi Kumar, V.Durga Prasad Rao Abstract |
89 |
|
16
|
Design and Applications of Decision Trees
-Amit Kumar Abstract |
94 |
|
17
|
An Efficient Priority Based Load Balancing Algorithm for Cloud Environment
-Harmandeep Singh Brar, Vivek Thapar Abstract |
99 |
|
18
|
An Efficient Service Broker Policy for Cloud Computing Environment
-Kunal Kishor, Vivek Thapar Abstract |
104 |
|
19
|
Hybrid Security and Fine-Grained Access Control for Personal Health Record in Cloud Computing
-P.Naresh Kumar,P.Venkateswara Rao Abstract |
110 |
|
20
|
Adaptive Contrast Binarization Using Standard Deviation for Degraded Document Images
-Jeena Joy, Jincy Kuriakose Abstract |
114 |
|
21
|
Health Care Analysis Based On Fuzzy Logic Control System
-M. Mayilvaganan, K.Rajeswari Abstract |
119 |
|
22
|
MAC in Cloud Security
-Jasjit Singh Samagh Abstract |
123 |
|
23
|
Embedded Optical Character Recognition On Tamil Text Image Using Raspberry Pi
-V. Ajantha Devi, Dr. S Santhosh Baboo Abstract |
127 |
|
24
|
Cloud Information Accountability Framework Based On the Notion of Information Accountability
-N V Sruthi, R Kumaran, Vikram Neerugatti Abstract |
132 |
|
25
|
Analysis Fault Tolerance Facts Involve In Business Work Based On Data Mining Techniques
-M. Mayilvaganan, S.Aparna Abstract |
138 |
|
26
|
Deployment of Information and Communication Technology Tools as a Means of Combating National Insecurity in Nigeria
-Duke Urhe-Otokoh Oghorodi Abstract |
142 |
|
27
|
A Review of Data Compression Technique
-Ritu, Puneet Sharma Abstract |
148 |
|
28
|
Path Computation Algorithm Using Delay & Bandwidth Constraint
-Shalley Tyagi, Rakesh Kumar Singh Abstract |
153 |
|
29
|
Privacy Preserving Two Layer Encryption Access Control In Public Clouds
-A Reddy Prasad, Gudivada Lokesh, N Vikram Abstract |
157 |
|
30
|
A Review: Clone Detection in Web Application Using Clone Metrics
-Harpreet Kaur, Rupinder kaur Abstract |
164 |
|
31
|
Internet Protocol Television (IPTV) and its Security Threats - An Overview
-V.Vasanthi, M.Chidambaram Abstract |
172 |
|
32
|
Scope of Efficiency for Association Rule Mining In Cloud Environment
-K.Mangayarkkarasi, M.Chidambaram Abstract |
176 |
|
33
|
Classifying Corner Defects from Square Ceramic Tile at Production Phase
-Ravindra Singh, Gyan Chand Yadav Abstract |
180 |
|
34
|
Encryption Algorithms - Parallelization
-Shweta Kumari, Abhishek Kumar Abstract |
184 |
|
35
|
Energy-Efficient Routing Protocol for Wireless Sensor Networks Using Efficient Data Replication and Load Balancing
-Pooja Yadav, Poonam Yadav, Vinit kumar, Dr. Ajay Agarwal Abstract |
192 |
|
36
|
Evaluation of Active Queue Management Algorithms
-Arsh Arora, Lekha Bhambhu Abstract |
197 |
|
37
|
Detection and Prevention of Black-Hole Attack in MANETS
-Rashmi, Ameeta Seehra Abstract |
204 |