IJCST ONLINE
DOWNLOADS
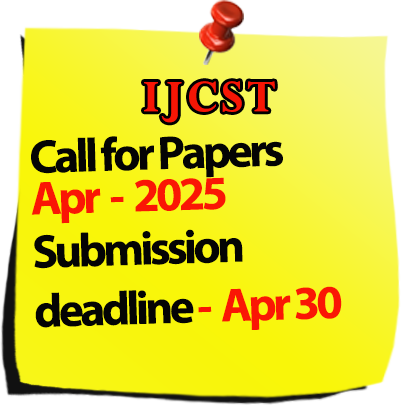
Call for Paper :

Welcomes Conference Proposals

International Journal of Computer Science Trends and Technology
IJCST-Volume 4 Issue 2 / Mar-Apr 2016
|
S.No
|
Title/Author Name
|
Page No
|
|
1
|
A Survey of Web Usage Mining: Concepts with Applications and its Future Scope
- Jitendra N. Shrivastava, Shivendra Pratap Singh Abstract |
1 |
|
2
|
Relay Nodes: Enhancing Network Lifetime and Throughput in Wireless Sensor Networks
- Navjot Singh, Amandeep Singh Abstract |
6 |
|
3
|
A Recommendation System for Online Products by Analyzing The Customer Feedback
- N. Rajganesh, R.Nandhini, G.Vinitha, E.Abinaya, M.Sumitha Abstract |
14 |
|
4
|
Survey of Computing and Future Trends
- Mbanzabugabo Jean Baptiste Abstract |
19 |
|
5
|
Data scheduling in VANET:A survey
- Sarita Negi, Smita Singh, S.K.Goel, Akshay Kumar Abstract |
25 |
|
6
|
Survey on Enhancing the Speed of Mapreduce Classification Algorithms Using Pre-Processing Technique
- Maya A.Gharat, Sharmila S.Gaikwad,Saurabh Suman Abstract |
32 |
|
7
|
Solutions of Cloud Computing Security Issues
- Jahangeer Qadiree, Mohd Ilyas Maqbool Abstract |
38 |
|
8
|
Innovative Technique of Improving Student Performance Using Data Mining Algorithm
- Rupali Chudasama, Prof. Amol Joglekar Abstract |
43 |
|
9
|
Help the Society in Selecting Their Best Life Insurance Cover (LIC) Using Data Mining Technique
- Prathama Nemalekar, Prof. Amol Joglekar Abstract |
49 |
|
10
|
Accountable Obliviously Transfer With Access Control
- Mrs.K.Aruna, Ms.S.Durgadevi Abstract |
54 |
|
11
|
Smart Supervised Method for Blood Vessel and Optic Disc Segmentation from Fundus Images
- P.Anu, T.Jeyaselvi, J.Johncy Eunice,M.Magie Pushpa Abstract |
58 |
|
12
|
Cloud Computing Security single to multicloud using AES Algorithm
- Miss.Kirti Sakhare, Miss.Swati Patil, Miss.Vijaya Shendage, Miss.Swati Kolhe Abstract |
66 |
|
13
|
A Lightweight Encryption Scheme for Network-Coded Mobile Ad Hoc Networks
- Mohammed Tarique, Rohan Raul, Khalil Pinjari, Pranay Patil, Rohit Shinde Abstract |
71 |
|
14
|
An Analytical Framework For Understanding Knowledge Sharing Process In Online Discussion Forum
- Jessima.B, Sowmiya.K, Kalpana.R, Amala Preethi.L, Mr.Barani Vijaya Kumar A.T Abstract |
76 |
|
15
|
App Blocker Using Access Control Mechanism In Android Mobile Phones
- Prof. Divya S, Ms. Vanitha S, Ms. Dakshana V M, Ms. Sharmila N Abstract |
79 |
|
16
|
Survey of Techniques for Improving the Quality of Image Obtained Using Jpeg Compression Algorithm
- Anand Mehrotra Abstract |
84 |
|
17
|
Information Security in Large Amount of Data: Privacy and Data Mining
- Prof. Harish Barapatre, Ms. Sampada Samel Abstract |
88 |
|
18
|
Store Hub an Android App
- Assist. Prof. Ansar Ahemad, Shakir Khan, Ajay Machhi, Ajay Baria, Akash Sabat Abstract |
100 |
|
19
|
Survey On Continuous User Identity Verification Using Biometric Traits for Secure Internet Services
- Neethu T.D , Ayana Ajith Abstract |
106 |
|
20
|
Malware Detection In Android By Network Behaviour Analysis
- Prof. Shanmuga Priya M, Ms. Soundarya S, Ms. Aashika S Abstract |
110 |
|
21
|
A Nowadays Protect Your Inbound /Outbound Data Packets Firewall Security Established In Network
- Yashpal, Aniruddha Dubey, Ashish Kumar Abstract |
114 |
|
22
|
Effective Hybrid Compressive Sensors Using Wireless Networks in Clustering Methods
- P.Sukumar, B.Sowmya Abstract |
118 |
|
23
|
Survey of VM Load Balancing Algorithm in Cloud Environment
- Er. Pooja, Er. Vivek Thapar Abstract |
122 |
|
24
|
Secure Data Aggregation in Wireless Sensor Network using Trust Model
- M.Suraj, B.Raja, T.Vengattaraman Abstract |
130 |
|
25
|
The Imperative of Education on National Development
- Umudjere Sunday Oghenebrorhie, Dr. Okogu Joel Otitie, Osah Mark Abstract |
138 |
|
26
|
A Study to Develop Server Virtualization Infrastructure in Educational Institutions with Cost Effective and Green Computing Approach
- Yogesh Madhukar Ghorpade, Prof. (Dr.) R. Kamatchi Abstract |
144 |
|
27
|
K-MED: An Algorithm of Uniform Clustering for Efficient Content-Based Image Retrieval
- Rashmi Chauhan, Shashank Kumar Som, Ankush Mittal Abstract |
151 |
|
28
|
EDHS Schedulability Analysis for Real-Time Multiprocessor Scheduling
- Rula Mreisheh, Mohammed Hijazieh Abstract |
157 |
|
29
|
Smart Event Management System
- Assist.prof. Khalil Pinjari, Khan Nur Abstract |
161 |
|
30
|
Civic Administration
- Shahbaz khan, Ajeet Mishra, Sharad Hari Dhavre, Sagar Patil Abstract |
165 |
|
31
|
A Methodology for the Usage of Side Data in Content Mining
- Priyanka S Muttur, Babruvan R. Solunke Abstract |
170 |
|
32
|
A Review on Various Techniques of Brain Tumor Detection
- Rajeshwari G.. Tayade, Miss. P. H. Patil, Miss. Prachi A. Sonawane Abstract |
179 |
|
33
|
A Review on Various Methodology of White Blood Cell Detection
- Miss. Prachi A. Sonawane, Mrs. A. N. Shewale, Miss. Rajeshwari G. Tayade Abstract |
180 |
|
34
|
RedBox-A Data Mining Approach for Improving Business Intelligence
- Tapan Nayak Abstract |
187 |
|
35
|
Efficient Smart Routing Protocol for Faithful Transmission Of Packet and Traffic Balancing (ESFTB)
- Sushma A, Dr. Premjyoti Patil, Dr. Shantakumar B Patil, Bhargava R Abstract |
192 |
|
36
|
Transmission of Data Using Li-Fi Technology
- Gaurav Singh, Santoshkumar Yadav, Essakkimuthu Nadar, Kumari Gowda Archana Nanade Abstract |
199 |
|
37
|
A Survey on Multiple Attribute Graph Indexing Methods
- Abilasha S, Remya G, Anuraj Mohan Abstract |
203 |
|
38
|
Enhanced Multimedia Information Retrieval on Web Using Text Based Query
- Meenakshi Alamelu S, Mannar Mannan J Abstract |
210 |
|
39
|
Energy Reduction Techniques in Cloud Computing: A Review
- Jasleen kaur, Navpreet Kaur Walia Abstract |
216 |
|
40
|
Remotely Control of Android Based OS Mobile Application
- Dhananjay Singh Abstract |
222 |
|
41
|
Software Testing Using CMM Level 5
- Dhananjay Singh Abstract |
233 |
|
42
|
Open Source Software a Study on BITCOIN
- Kunwar Uday Singh, Harshit Sinha, Dr. Ajay S. Singh, Thirunavukkarasu K Abstract |
243 |
|
43
|
Virtual Keyboard Using BLOB Analysis
- Antara Kanade, Ayesha Shaikh, Mabel Fernandes, Shubhangi Chikhalthane Abstract |
247 |
|
44
|
Precising the Characteristics of IP-FPM Algorithm
- Dr. K.Kavitha Abstract |
252 |
|
45
|
A Proposed Approach for Cloud Storage Optimization with Authorized Byte level De-duplication
- Ruchi Agrawal, Prof. D. R. Naidu Abstract |
259 |
|
46
|
Comparative Study of Routing Protocols in Mobile ADHOC Networks
- Muhammad Safdar,Izaz Ahmad Khan, Fazlullah Khan, Farman Ullah, Syed Roohullah Jan Abstract |
264 |
|
47
|
Face Recognition Using Principal Component Analysis Based Feature Space by Incorporating with Probabilistic Neural Network
- Muhammad Tahir, Shahid Akbar Shahzad, Maqsood Hayat, Nazia Azim Abstract |
276 |
|
48
|
Offsite One Way Data Replication towards Improving Data Refresh Performance
- Nazia Azim, Yasir Qureshi, Fazlullah Khan*, Muhammad Tahir, Syed Roohullah Jan, Abdul Majid Abstract |
285 |
|
49
|
Superseding Nearest Neighbor Search in Wireless Network using Delaunay Triangulation
- Shweta Purohit, Ajay Mathur Abstract |
297 |
|
50
|
Review: Apache Spark and Big Data Analytics for Solving Real World Problems
- Mrs. Dipali Dayanand Ghatge Abstract |
301 |
|
51
|
Effect of Performance In Heterogeneous Traffic In Opportunistic Networks
- Gopinath A R, Sithara K J Abstract |
305 |
|
52
|
REAL: A Reciprocal Protocol for Privacy in Wireless Communication Networks
- Annapurna B P, Bhuvana N, Harshitha Rajendra, S Renukadevi Abstract |
309 |
|
53
|
Factor of Success in Software Development: Effort Prediction
- Akshika Aneja Abstract |
312 |
|
54
|
Messaging Application Based On Android for Visually Challenged People
- Akshika aneja Abstract |
315 |
|
55
|
Energy Conservation and Effective Data Transmission Using the Selective Data Dissemination Strategies
- Himani Sharma, Jatinder Pal Sharma Abstract |
319 |
|
56
|
Cognitive Computing: Building a Smarter Planet
- Sapandeep Kaur, Ikvinderpal Singh Abstract |
325 |
|
57
|
A Survey Report on Internet of Things Applications
- Sapandeep Kaur, Ikvinderpal Singh Abstract |
330 |
|
58
|
Reducing Bug Triage in Software Development in Data Reduction
- M. Ahilandesware, J. Prathiba Abstract |
336 |
|
59
|
Internet of Things (IOT) Vision in Gulf Future Business
- Waleed Bamousa Abstract |
340 |
|
60
|
Light fidelity (LiFi): Future of Wireless Technology
- Akshika Aneja, Arvind Sharma Abstract |
343 |
|
61
|
A Study of Security Issues Related With Wireless Fidelity (WI-FI)
- Akshika Aneja, Garima Sodhi Abstract |
346 |
|
62
|
An Analysis on Types of Speech Recognition and Algorithms
- Dr.V.Ajantha Devi,Ms.V.Suganya Abstract |
350 |
|
63
|
Remove Noise from Scanned Handwritten De-Graded Document Images Using Various Approaches
- Kuljeet Singh, Gurinder Singh Abstract |
356 |
|
64
|
Safety and Threats in Cloud Computing Survey paper
- Sultan Alfajhan Abstract |
362 |